Microsoft ends support for Internet Explorer on June 16, 2022.
We recommend using one of the browsers listed below.
- Microsoft Edge(Latest version)
- Mozilla Firefox(Latest version)
- Google Chrome(Latest version)
- Apple Safari(Latest version)
Please contact your browser provider for download and installation instructions.
October 27, 2021
NTT Corporation
NEC Corporation
NTT and NEC have developed Supply Chain Security Risk Reduction Technology for ICT Infrastructure
NTT Corporation (headquartered in Chiyoda-ku, Tokyo: Jun Sawada, President and CEO; "NTT") and NEC Corporation (headquartered in Minato-ku, Tokyo: Takayuki Morita, President and CEO; "NEC") have developed Security Transparency Assurance Technology, which is the core technology for realizing the Trusted Network Concept. Security Transparency Assurance Technology, which aims to reduce supply chain security risks, ensures security transparency throughout the supply chain by sharing system configurations and risks of network devices and information systems that constitute ICT infrastructure, including the Fifth Generation Mobile Communication System (5G), Local 5G, and IOWN *1, an innovative network technology.
NTT and NEC entered into a capital and business alliance in June 2020 for the purpose of joint research and development and the global rollout of ICT products utilizing innovative optical and wireless technologies *2, and are developing internationally competitive products and technologies. This initiative is a part of the alliance.
The latest results of this technology will be exhibited in the NTT R&D Forum - Road to IOWN 2021 *3, which is scheduled to be held from November 16 to 19 in 2021.
1. Background
As the digital transformation (DX) of society and industry accelerates, supply chain security risks, such as intrusions of unauthorized software (malware, etc.) through the supply chain related to procurements, maintenances, and operations, of network devices and information systems constituting the ICT infrastructure, and unauthorized intrusion into networks and information systems through organizations with weak cybersecurity facilities, have become apparent.
As a risk countermeasure, the suppliers of network devices and information systems (e.g., network device vendors, system integrators, etc.) in the supply chain attest safety and for the customers confirm it. At present, however, it is technically difficult to indicate and confirm it and we have to rely on the trust between the suppliers and the customers, and both two have to take risks on their own.
2. Technology
Security Transparency Assurance Technology, which is at the core of the realization of trusted networks, is a technology that ensures transparency regarding the security of ICT infrastructures by sharing information (hereinafter referred to as "device information") that visualizes the configuration and risks of communications devices and systems that constitute ICT infrastructure.
(1) Visualizes software configurations in the network devices continuously through the supply chain (e.g., manufacturing, shipping, deployment and operation) and generates the device information including the inspection results of presence of backdoors and illegal components.
(2) The device information enables high-quality risk analysis and monitoring based on its completeness and accuracy, and the transparency of the device information will be maintained at a high level through continuous updates of it.
(3) Sharing the device information among organizations that form the supply chain enables it possible to take countermeasures against security risks, to take advantage of transparency and to improve security at all phases and at all organizations in the supply chain.
This technology is realized by the following elemental technologies possessed by NTT and NEC.
[NTT] Configuration analysis technology for visualizing software configuration of devices
[NEC] Backdoor inspection technology to detect illegal functions in device software
[NEC] Automated cyber-attack risk assessment technology for visualizing attack routes in systems *4
Using this technology, customers can check the presence of suspicious components by referring to the device information during procurement and operation *5, and suppliers can explain the risk of contamination with unauthorized components objectively. In addition, customers can take a prompt action by identifying risks and impacts using device information when a new software vulnerability is found.
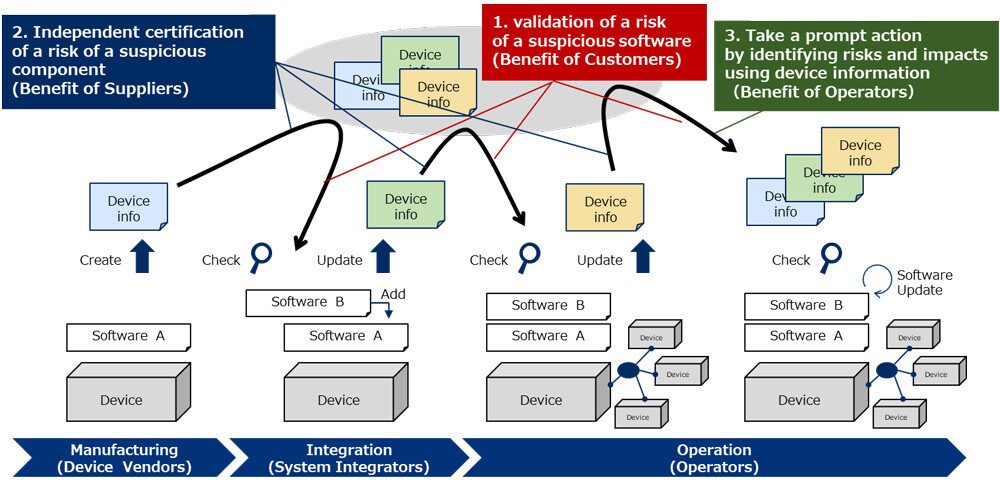 Figure 1: Security Transparency Assurance Technology Overview and Benefits
Figure 1: Security Transparency Assurance Technology Overview and Benefits
3. Future Development
We are planning to carry out technical validation using this technology at local 5G within fiscal 2021 to verify the effectiveness of each elemental technology and identify issues.
Furthermore, we aim to set up a consortium of players involved in the construction and operation of trusted networks, such as communication device vendors, system integrators, and user companies. By utilizing this technology, we will establish countermeasures for supply chain security risk that is difficult by a single player.
Contact
NTT Corporation
Public Relations Office
Tel:+81-3-5205-5550
NEC Corporation
Public Relations Office, Corporate Communications Division
Tel:+81-3-3798-6511
Reference
- IOWN (Innovative Optical and Wireless Network)
A future communication infrastructure that realizes a smart world and utilizes the latest optical and information processing technologies.
URL:https://www.rd.ntt/e/iown/ - Alliance for Joint Research and Development and Global Rollout of ICT Products Utilizing Innovative Optical and Wireless Technologies
URL:https://group.ntt/en/newsrelease/2020/06/25/200625b.html - NTT R&D Forum - Road to IOWN 2021
URL:https://www.rd.ntt/e/forum/ - Technology provided by NEC to visualize system security risks and the effects of countermeasures.
Cyber Attack Route Assessment Service
URL:https://jpn.nec.com/press/202106/20210629_01.html - It will make it possible to easily respond to supply chain security requirements (security inspection at device procurement and operation, risk reduction, etc.) in guidelines set by government agencies in various countries.
Information is current as of the date of issue of the individual press release.
Please be advised that information may be outdated after that point.
NTT STORY
WEB media that thinks about the future with NTT